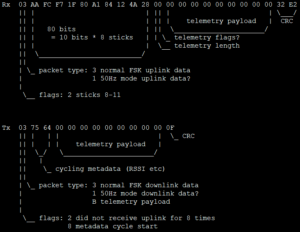
[FPV] Analysis of TBS Crossfire, reverse engineering the air link
I started flying FPV quads for a bit of freestyle flying about two years ago. Not very skilled, but also flying every now and then, so no real focused learning. Quickly I jumped onto the TBS Crossfire train and bought a TBS Tango 2 and...

[FPV] Eachine EV800 mods
I own FPV goggles from Eachine and have been very happy with them. Yes, you look like an idiot with a brick on your forehead, but the antennas make you look more like a Johnny 5 fan, which is cool again. At least was 3...